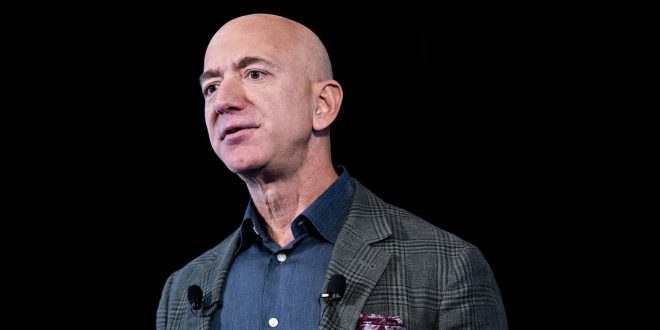
On November 8, 2018, Amazon CEO Jeff Bezos received an unexpected text message over WhatsApp from Saudi Arabian leader Mohammed bin Salman. The two had exchanged numbers several months prior, in April, at a small dinner in Los Angeles, but weren’t in regular contact; Bezos had previously received only a video file from the crown prince in May that reportedly extolled Saudi Arabia’s economy. The November text had an attachment as well: an image of a woman who looked like Lauren Sanchez, with whom Bezos had been having an unreported affair.
That message appears to have been a taunt; American Media Inc., publisher of The National Inquirer, would several months later make details of the affair public. But it’s the initial contact, in May, that has set off another firestorm with MBS at the center. That video file was loaded with malware, investigators now say. The crown prince’s own account had been used to hack Bezos’ phone.
Such brazen targeting of a private citizen—the richest man in the world, no less—is alarming to say the least. It underscores the dangers of an unchecked private market for digital surveillance, and raises serious questions about other prominent US figures who have known relationships with the crown prince, like White House adviser Jared Kushner and President Donald Trump himself.
“This reported surveillance of Mr. Bezos, allegedly through software developed and marketed by a private company and transferred to a government without judicial control of its use, is, if true, a concrete example of the harms that result from the unconstrained marketing, sale, and use of spyware,” United Nations special rapporteurs David Kaye and Agnes Callamard said in a statement. Details provided by the UN suggest that the malware originated from a private vendor, such as Israel’s NSO Group or the Italian Hacking Team. The tie to MBS was first reported Tuesday by The Guardian.
Bezos became a Saudi target not because of Amazon but for his ownership of The Washington Post, which had published a series of critical stories about the kingdom. The November text from MBS came one month after Saudi officials murdered Post columnist and Saudi dissident Jamal Khashoggi inside the country’s Istanbul consulate. The UN probe into the attack on Bezos is based at least in part on a forensics analysis commissioned by Bezos himself and completed by FTI Consulting, a cybersecurity consulting firm. The findings are not definitive, and the firm ranked them at medium to high confidence. Similarly, the UN made clear that while its investigation indicated these results, attribution is not certain.
“All FTI Consulting client work is confidential. We do not comment on, confirm, or deny client engagements or potential engagements,” the firm told WIRED in a statement.
The Saudi embassy denied the allegations on Twitter Tuesday evening: “Recent media reports that suggest the Kingdom is behind a hacking of Mr. Jeff Bezos’ phone are absurd. We call for an investigation on these claims so that we can have all the facts out.”
According to the UN’s findings, the Saudi regime began exfiltrating large amounts of data from Bezos within hours of sending the tainted MP4 video file. FTI Consulting found that six months before the video download, an average of about 430 kilobytes of data came from Bezos’ phone per day, a small amount. Within hours of receiving the video, that number rose and the phone started averaging 101 megabytes for months afterward. The UN reports that this number sometimes even jumped into the gigabyte range, several orders of magnitude over the pre-hack baseline—indicating data exfiltration through malware.
The UN report points to Pegasus malware, developed by the cyberarms dealer NSO Group, which has adapted it for use on numerous iOS and Android versions over the past four years. Saudi Arabia first bought Pegasus from NSO Group in November 2017, according to the UN. Investigators suggest Galileo, a Hacking Team product, as another possibility. Analysis of those tools by third-party and academic researchers have shown that both are capable of compromising a device and accessing almost any data on it, from text messages, calls, contacts, and emails to apps, browsing history, and even location data.
NSO Group denied in a statement that its tools were used in the attack. “As we stated unequivocally in April 2019 to the same false assertion, our technology was not used in this instance,” the firm said. “Our technology cannot be used on US phone numbers. Our products are only used to investigate terror and serious crime. Any suggestion that NSO is involved is defamatory.”
The UN alleges that during the same period that the Saudi regime had access to Bezos’ phone, it also targeted Khashoggi’s associates and other pro-human rights dissidents using mobile malware developed by NSO Group. The actions fit with Saudi Arabia’s broader pattern of targeting activists. In November, the Justice Department charged two Twitter employees with abusing internal systems to steal information on Saudi Arabia’s behalf.
Saudi Arabia appears to have simultaneously launched an online disinformation campaign to discredit Bezos. In November 2018, the top-trending hashtag on Twitter in Saudi Arabia was “Boycott Amazon,” the UN notes. The campaign abruptly stopped in April 2019, after an investigator working for Bezos accused the Saudis of hacking the executive’s phone. It then picked up again in October, after Bezos attended a memorial event for Khashoggi.
While private exploit brokers like NSO Group often describe themselves as forensic analysis firms, tools like Pegasus have a track record of being used for offensive hacking. In fact, analysts used such tools to analyze Bezos’ phone in the wake of the breach. Doing so proved challenging, given the sophistication of the attack. By the time a “physical analyzer” from the Israeli company Cellebrite vetted the device, there were no traces of malware. An audit of nearly 300,000 directories, sub-directories, and file names similarly yielded no evidence of iOS jailbreaking tools.
It was also difficult to analyze the video sent from the crown prince’s account for signs of malware, because both the file itself and the downloader were encrypted. And the UN notes that WhatsApp’s own end-to-end encryption also created challenges. Cellebrite’s software platforms for analyzing device traffic and network logs did pinpoint, though, when Bezos’ phone began hemorrhaging data.
“It sounds like whatever implant they had self-destructed and wasn’t there when they went for the forensics,” says Dave Aitel, chief security technology officer at the secure infrastructure firm Cyxtera and a former NSA analyst. “It seems about right that you would have a self-destruct capability on any real implant. And US investigators probably have other classified information that validates their attribution.”
It’s not clear what other information the hack may have gleaned about Bezos or Amazon’s business. The incident also puts further scrutiny on an already controversial private cyberarms industry. At the end of October, WhatsApp and its owner, Facebook, sued NSO Group over alleged attacks on more than 1,000 of its users—a first effort to curb rampant growth of the private exploit industry. The complaint noted that at least some of NSO Group’s infrastructure is hosted by Amazon Web Services. Additionally, Facebook patched a vulnerability in November that “could be triggered in WhatsApp by sending a specially crafted MP4 file to a WhatsApp user.” It is unclear if this bug was exploited to target Bezos, but it’s a reminder that such bugs can exist in even the most seemingly innocuous features of an app like WhatsApp.
Saudi Arabia’s apparent targeting of one of the world’s most powerful businessmen raises questions about the kingdom’s communications with US officials, including Jared Kushner, President Trump’s son-in-law and adviser on the Middle East. Kushner has reportedly exchanged personal messages with MBS, and has been known to use WhatsApp to talk with foreign leaders. Kushner was issued a top-secret security clearance, even after concerns were raised by White House and intelligence officials about the risk of foreign influence.
Meanwhile, President Trump is known for using personal, consumer-grade smartphones, resisting advice from the White House’s IT and cybersecurity staff to use only a hardened device. That such a simple, elegant attack could snag Jeff Bezos underscores just how at-risk Trump has been. Countless actors around the world would want nothing more than unfettered access to his phone; all it would take to get it is making him click on a video or link.
Though the incident will raise awareness about the growing threats of the private cyberarms industry and potential abuse of its products, it seems unlikely that it will come with any immediate reprisals. The UN says it will continue its investigations into both the Khashoggi murder and the rampant use of spyware; it seems there’s no shortage of details still to uncover.
More Great WIRED Stories
- The Mandalorian is the only smart soldier in the Star Wars galaxy
- The millennial meaninglessness of writing about tech
- Homelessness in the living rooms of the rich
- How Hong Kong’s protests turned into a Mad Max tableau
- Why the “queen of shitty robots” renounced her crown
- 👁 The secret history of facial recognition. Plus, the latest news on AI
- 🎧 Things not sounding right? Check out our favorite wireless headphones, soundbars, and Bluetooth speakers
 The Argus Report Read about it!
The Argus Report Read about it!